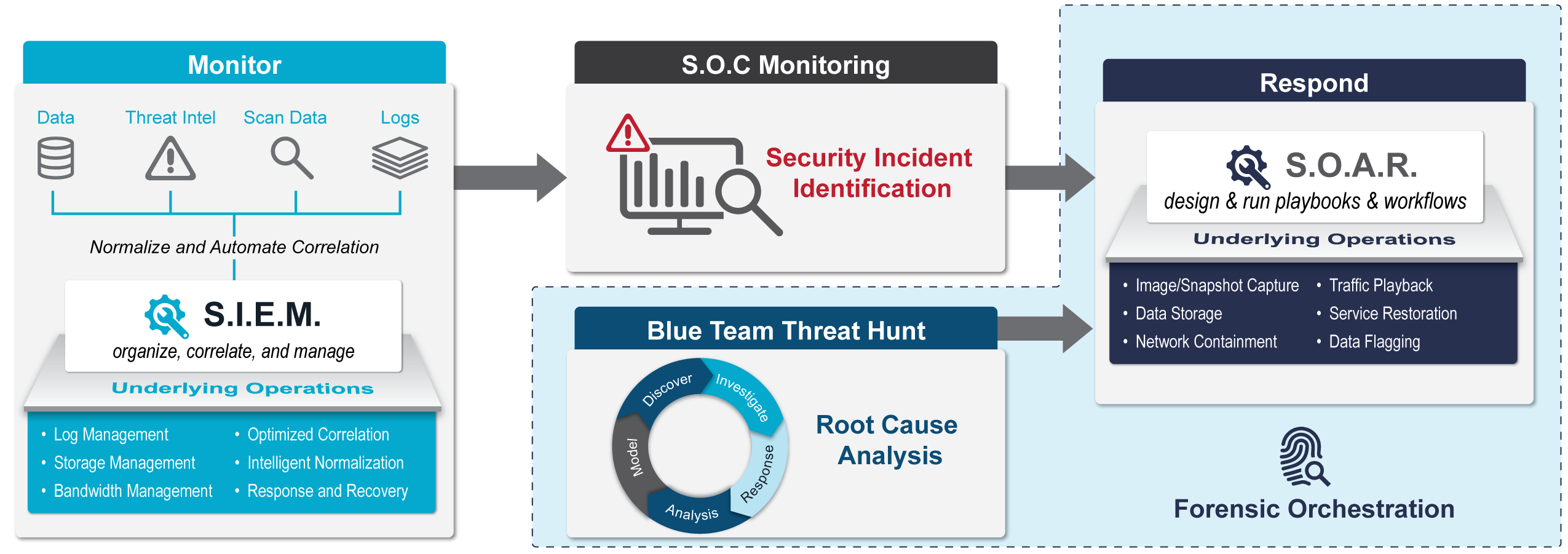
Forensic Orchestration
Forensic Orchestration is a next generation organizational cybersecurity capability that incorporates modern operations virtualization, automation and data storage management with security processes, playbooks, deployed agents and monitoring systems. Forensic Orchestration is used to capture and preserve endpoint, network and environment state data for use in root cause analysis, in-house digital forensic analysis, 3rd party digital forensic analysis, law enforcement digital forensic analysis or for use as evidence in criminal proceedings.
Mission Impact
- Enable integration of forensic investigation into incident response
- Preserve key evidence of maleficence or intrusion
- Reduce the time elapsed to capture digital evidence from the first detected indicator of compromise
- Streamline the technical component of root cause analysis to reduce the time to produce actionable executive level reporting
- Reduce visibility of insider threat investigations
Features
- Captures event related evidence in a legally compliant format, preserving chain of custody
- Preserves real time evidence for later root cause analysis and security analysis
- Links security incident response and operations incident response practices through common tools, techniques and procedures
Use Cases
- Organizations with operations and security monitoring teams working in parallel
- Organizations looking to establish security Blue Team or Security Hunt Teams
- Organizations who may rely on third party investigators (USCERT, contracted incident response consulting services, law enforcement, etc.) following security incidents
- Organizations required maintaining a legal chain of custody and legally acceptable digital forensic artifacts
- Organizations looking to reduce the manual operations workload of security incident case management
Infographic
Considerations
- Recent advances in virtualization and containerization including self-healing services and software-defined data centers could lead to an inadvertent destruction of digital evidence of compromise.
- Forensic Orchestration focuses more on the maturity of tool integration and process automation, and less on selection of new tools and platforms.
- Due to the separation of duties for security and administrative teams, internal investigations are difficult to perform without alerting a privileged user that may be under investigation. Adding automation and orchestration to the digital evidence capture process can deconflict these security and operational requirements.
ValidaTek’s Process
- Survey enterprise tools currently in use by operations and security
- Where possible, leverage existing methods of automation for storage duplication, image capture, memory scraping, log capture, and digital capture of artifacts and evidence
- Supplement existing capabilities with digital forensic tools
a. Leverage NIST Forensic Tool Testing Program
b. Leverage NIST Cloud Computing Forensic Science studies
c. Use Open Source tools when possible - Tie automation into operations and security event monitoring processes and systems
- Align capture and storage practices with enterprise retention policy and access control with digital forensics best practices and enterprise roles based security and separation of duties
For More Information
Email: [email protected]
Phone: 703-972-2272